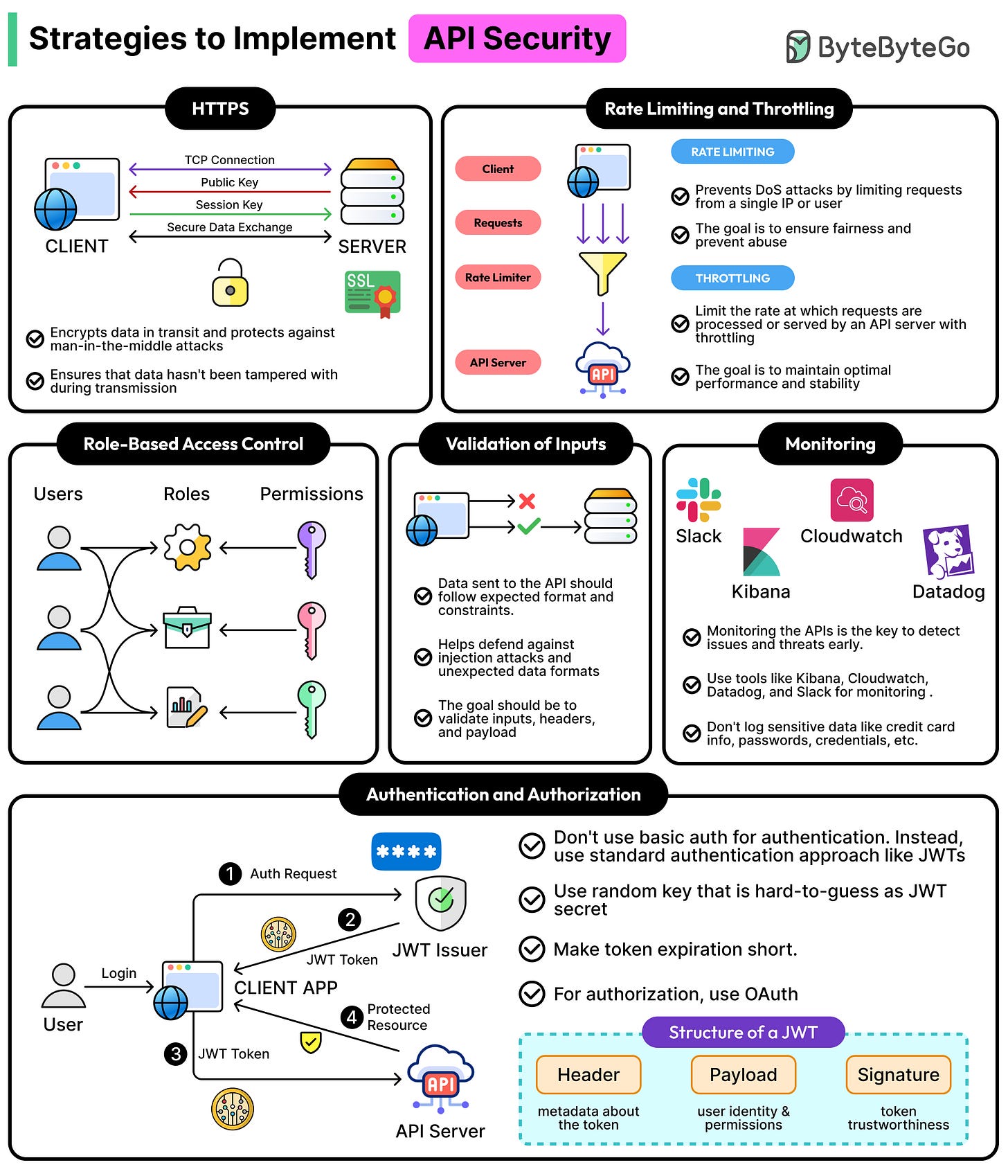
How to Implement API Security
Most APIs that ship to production have some security in place. Most of the time, HTTPS is enabled, an API key is required, and maybe there’s even a quick code review before deployment.
By most measures, the box is checked. However, a checked box and a secure API are not the same thing. A common and costly example is an API that validates credentials correctly on every request, but never checks whether those credentials grant access to the specific resource being requested. In other words, authentication works, but there’s no proper authorization.
Such an API could not be called secure, but sometimes nothing in the happy path would reveal the issue until someone found the gap.
This is what makes API security genuinely tricky. The strategies may be well-documented, but understanding when to use a particular strategy can be confusing. In this article, we will look at various API security strategies and try to understand which strategy works in which scenario.