EP89: What does ACID mean?
This week’s system design refresher:
ByteByteGo’s TikTok / Instagram Reels Channel
Why is JWT popular? (Youtube video)
What does ACID mean?
Internet traffic routing policies
😘 Kiss bugs goodbye with fully automated end-to-end test coverage (Sponsored)
If you've tried to build automated test coverage in-house, you know it takes years to scale. Try QA Wolf instead - they get web apps to 80% test coverage in just 4 months. They will create and maintain your test suite in open-source Playwright (no vendor lock-in, you own the code), and provide unlimited parallel test runs on their infrastructure.
The best part: QA Wolf saves you money. QA Wolf has multiple case studies of customers saving at least $200k/year in QA engineering and infrastructure costs.
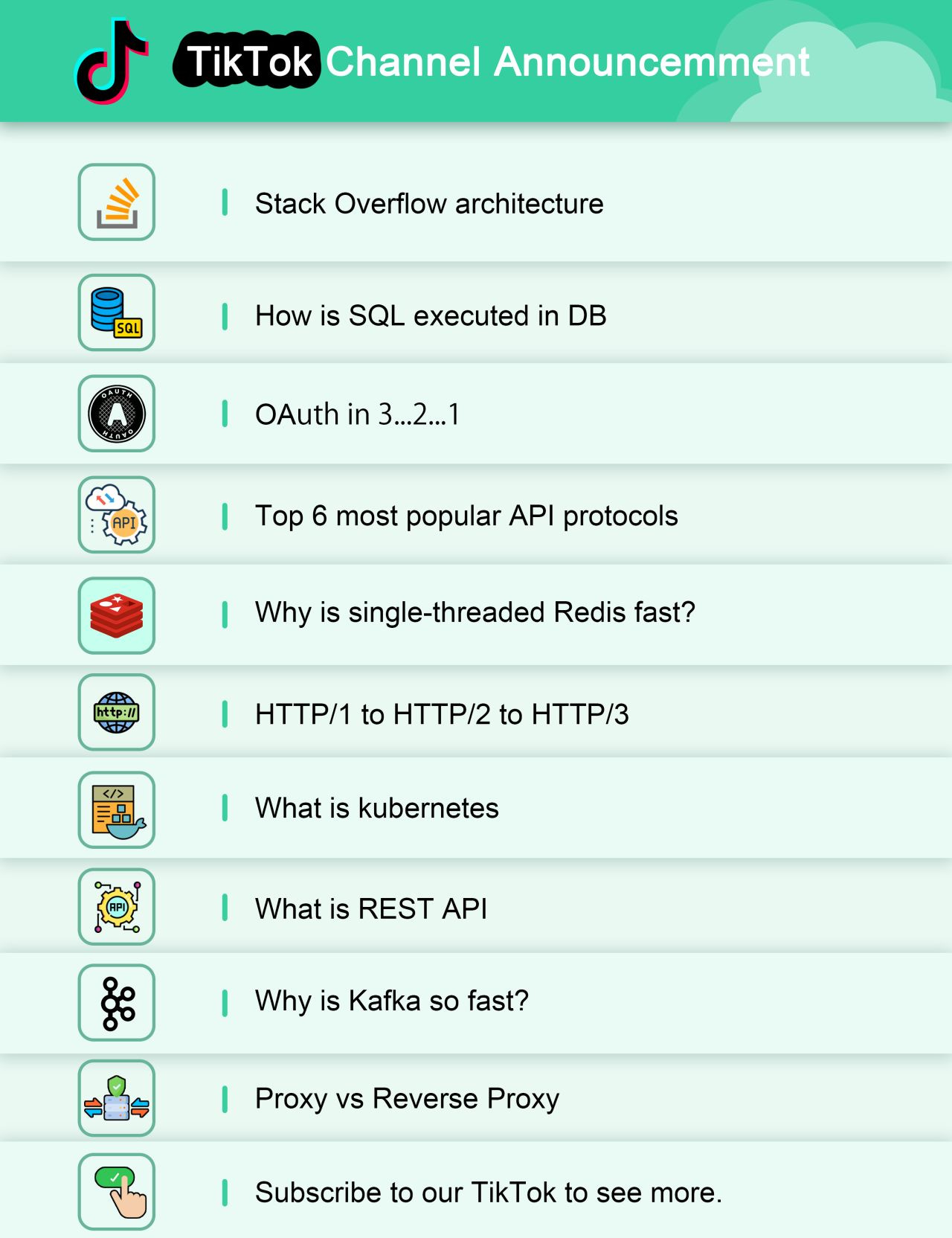
*BIG* announcement: we’ve re-launched our TikTok / Instagram reels channel!
The first video is already live, and we'll try to post new videos every week.
We'll be covering a wide range of topics, including:
Stack Overflow's shocking architecture
HTTP/1 -> HTTP/2 -> HTTP/3
How to avoid double charges?
Why is Kafka fast?
How to choose the right database?
What is REST?
What is GraphQL
What is gRPC
Proxy Vs Reverse Proxy
And more…
If you're interested in seeing more, make sure to subscribe to our TikTok channel and Instagram channel.
We are new to creating short videos and would appreciate your feedback :) Thank you.
Why is JWT popular?
Latest articles
If you’re not a paid subscriber, here’s what you missed this month.
To receive all the full articles and support ByteByteGo, consider subscribing:
What does ACID mean?
The diagram below explains what ACID means in the context of a database transaction.
Atomicity
The writes in a transaction are executed all at once and cannot be broken into smaller parts. If there are faults when executing the transaction, the writes in the transaction are rolled back.
So atomicity means “all or nothing”.Consistency
Unlike “consistency” in CAP theorem, which means every read receives the most recent write or an error, here consistency means preserving database invariants. Any data written by a transaction must be valid according to all defined rules and maintain the database in a good state.Isolation
When there are concurrent writes from two different transactions, the two transactions are isolated from each other. The most strict isolation is “serializability”, where each transaction acts like it is the only transaction running in the database. However, this is hard to implement in reality, so we often adopt loser isolation level.Durability
Data is persisted after a transaction is committed even in a system failure. In a distributed system, this means the data is replicated to some other nodes.
Internet Traffic Routing Policies
Internet traffic routing policies (DNS policies) play a crucial role in efficiently managing and directing network traffic. Let's discuss the different types of policies.
Simple:
Directs all traffic to a single endpoint based on a standard DNS query without any special conditions or requirements.Failover:
Routes traffic to a primary endpoint but automatically switches to a secondary endpoint if the primary is unavailable.Geolocation:
Distributes traffic based on the geographic location of the requester, aiming to provide localized content or services.Latency:
Directs traffic to the endpoint that provides the lowest latency for the requester, enhancing user experience with faster response times.Multivalue Answer:
Responds to DNS queries with multiple IP addresses, allowing the client to select an endpoint. However, it should not be considered a replacement for a load balancer.Weighted Routing Policy:
Distributes traffic across multiple endpoints with assigned weights, allowing for proportional traffic distribution based on these weights.
Over to you: Which DNS policy do you find most relevant to your network management needs?






Wow It's fantastic :)
I love your diagrams? Do you use specific tool or?